For several months, we have been working to implement support for new cryptographic methods in Proton Mail that give users a faster experience with equal or better security. Today, we’re excited to announce that elliptic curve cryptography is now available in all our applications for web, mobile, and desktop(new window) (Bridge).
For reasons we explain below, elliptic curves are rapidly replacing RSA as the gold standard for public-key cryptography. You may already be using it in other services, such as WhatsApp; Chrome, Firefox, and Opera browsers; and Tor. In March 2018, we released(new window) elliptic curve cryptography in OpenPGPjs(new window), the open-source encryption library we maintain, allowing hundreds of apps to take advantage of next-generation cryptography. In August, OpenPGPjs passed an independent security audit(new window), paving the way for implementation in Proton Mail.
Why switch to elliptic curve cryptography?
For decades, RSA was the only game in town, rooted in a powerful mathematical concept: multiplying large prime numbers is easy, but factoring the product is hard. But as computers get faster, RSA encryption requires bigger and bigger numbers to stay secure. Large numbers slow things down, especially on mobile devices with less computing power.
So, over the last few years, more products and protocols(new window) have been implementing a more efficient cryptographic system called elliptic curve cryptography. ECC also relies on a mathematical equation, but it requires much smaller numbers to accomplish the same level of security. For a more detailed explanation of how this kind of cryptography works, Ars Technica has published a useful summary(new window).
Using elliptic curve cryptography, the processes of key generation, encryption, and decryption become dramatically faster. That saves processing power (allowing you to log in and load emails faster), memory (freeing up space for other apps to work), and energy (giving you longer battery life).
Elliptic curve cryptography is very secure
Public key cryptography — both high-bit RSA and elliptic curves — is extremely safe. As with any encrypted system, the only practical way to backdoor it is to exploit weaknesses in its implementation, not the math itself. With ECC, there are only two known attacks, one(new window) that takes advantage of random number generators and another(new window) that exploits things like device power consumption to glean clues about the keys. Both of these are well understood and were mitigated years ago.
We have chosen a particular elliptic curve system known as X25519, which is fast, secure, and particularly resistant to timing attacks(new window). It’s simple to implement and, for what it’s worth, isn’t the subject of any patent claims. (For advanced users, you can find a technical explanation of this decision at the bottom of this article.)
Some users may also be curious about quantum computers, which will be insanely fast and promise to upend existing encryption systems. Elliptic curve cryptography in its current form would not stand a chance against a quantum computer. But such technology is still at least several years away, and just as Proton Mail has adapted to the new ECC standard, we will continue to evolve alongside new challenges. There is active research today into quantum-resistant encryption algorithms which we are following closely.
How to use the new keys in Proton Mail
Over time, ECC keys will become the default for all new addresses in Proton Mail. If you already have a Proton Mail account, you can upgrade your RSA keys for each email address now. (You will still be able read emails encrypted with the old keys, provided you do not delete them.)
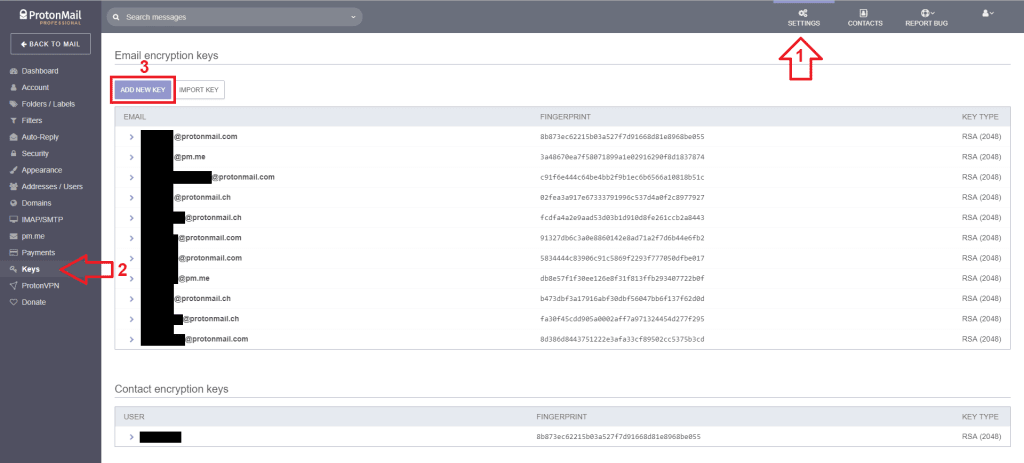
Log in to your account at mail.proton.me, click on Settings, and open the Keys page. Click on the “Add New Key” button and select the address for which you want to add ECC keys.

Then select:
State-of-the-art X25519 (Modern, fastest, secure)
And click on “Generate Keys”. You will be asked to enter your account password.

Next, click on the arrow next to your email address to reveal the key details. In the ECC key row, click on the dropdown menu and select “Make Primary.” This will make your new ECC the default key for this email address.

It is extremely important that you DO NOT DELETE YOUR OLD RSA KEYS. If you do, you will lose the ability to decrypt all your existing emails. Simply leave your old keys active; they will be used to decrypt old messages.
If you wish to continue using RSA encryption, your emails will still be safe, but your mailbox might move slower, especially on mobile devices. For the vast majority of users, ECC is the better method. (Some advanced users who receive PGP emails from non-Proton Mail users may decide to stay with RSA keys for a particular email address.)
We are excited to give you access to the latest advances in cryptography, and we look forward to hearing your feedback. You can find us on Twitter(new window) or engage with our community on our subreddit(new window). For help with your account, our support team(new window) is always available.
Best Regards,
The Proton Mail Team
Technical note
We are aware of the issues brought up here(new window) and here(new window). As mentioned in this one here(new window), we are already considering to switch to an implementation in WebAssembly to mitigate the possibility of timing attacks.
However, it is important to note that Curve25519 is a Montgomery curve and therefore these potential timing differences are far less trivial to exploit, as mentioned in the links above.
In our mobile and desktop apps, where timing attack resistance is easier to achieve, the X25519 implementation is already constant-time.
As some people have pointed out, the NIST P-256 curve is supported by Web Crypto, which should be constant-time. However, Curve25519(new window) is considered to be more modern, safer, and less prone to implementation errors than P-256, which is particularly important because many of our users receive email encrypted by implementations outside of our control.
Once they are generated, keys are controlled by our users and not easily updated, so we wanted to make a future-proof choice of curve. Once we have X25519 in WebAssembly, we’ll have the best of both worlds: the best curve available, in constant time.
Get a free secure email account from Proton Mail.
We also provide a free VPN servi(new window)ce(new window) to protect your privacy.
Proton Mail and Proton VPN are funded by community contributions. If you would like to support our development efforts, you can upgrade to a paid plan. Thank you for your support.














