Businesses are increasingly dealing with the fallout from cybercrime: The number of attacks is on the rise(new window) and the damage done is growing exponentially. One of the most common vulnerabilities for organizations are their passwords. Since they are your point of entry into an account, they are also the weakest point in your security infrastructure.
The first step to protect this is to have strong passwords, and the best way to enforce that is by having a strong password policy for your team. Below we go over what we think are the most important parts of any good password policy.
Use random passwords with a minimum length
Your password policy should be clear that all passwords must be fully randomized — so created by using a password generator, not a human mind. This is because humans will generally make up passwords that are easy to remember, rather than made to withstand attack. As a result, they are vulnerable to brute-force attacks, in which attackers will use software to “guess” users’ passwords.
Randomization isn’t the only way to create strong passwords. Another way to increase password strength is to simply make a password longer, at least 16 or so characters, though more is better. This is again to make things harder for hackers, as the longer the password, the more work it is for them to guess it.
A note on passphrases
Random passwords do come with a downside: namely that they are very hard to remember. There are several ways around this issue, but the simplest is to choose an approach that combines password length and memorization. Passphrases are perfect for this.
We go into more detail in our article comparing passphrases vs. passwords, but in short, passphrases are long chains of easily remembered words, so something like mortician profusely decent easeful. The length makes it hard to crack, while it’s still easy to remember. A passphrase is great for any account, but the primary use case is to unlock your password manager, which we’ll discuss further down.
Never reuse passwords
Another important thing that should be part of any password policy is that you should never reuse passwords. This means all your accounts should have their own unique passwords, and you should never recycle old passwords. For every new account you create, you need to generate a new, random password.
The reason for this is something called credential stuffing, where a hacker will take all the logins leaked during a large breach and try hundreds of sites to see if they will work there, too. It’s a serious risk, too, implicated in high-profile data leaks. In one case, hackers stole a Dropbox admin’s credentials and then used them to get into the company’s GitHub pages, wreaking all kinds of havoc.
This type of attack is very common, but you can render it inconsequential as long as you never reuse passwords, and make sure your team members don’t, either.
Enable two-factor authentication (2FA)
If passwords protect your accounts, two-factor authentication, better known as 2FA, can protect your passwords. If your password is the first factor, the second factor is a temporary code, usually generated by an app on your phone (there are variants using SMS, but they aren’t very secure(new window)). When you access an account, you will need to enter both the password and the code from the 2FA app.
Using 2FA means that even if somebody unauthorized were to get access to your password, they would also need to have the phone or other device that has your 2FA app on it to gain entry to your account. 2FA is the best way to defend against phishing attacks. It’s a powerful tool, but sadly underutilized.
Use a password manager to ensure compliance
Though a good password policy may differ across different teams and companies, these elements are vital to the security of any organization:
- Random passwords
- Long passwords
- Unique passwords
- 2FA
Of course, this brings to mind another issue, namely how you’re going to manage it all. Remembering long, random passwords is practically impossible — that’s their strength, after all — and manually keeping track of them on a piece of paper is not secure.
To make sure your team actually implements your password policy, they’ll need a password manager, a piece of software that can store your passwords for you.
A good password manager will not just store passwords, but also have a built-in password generator to create random passwords of any length whenever you need them. It will also autofill passwords whenever you log in to a site where you have an account, making password managers not just vital to security, but a massive improvement to your digital quality of life.
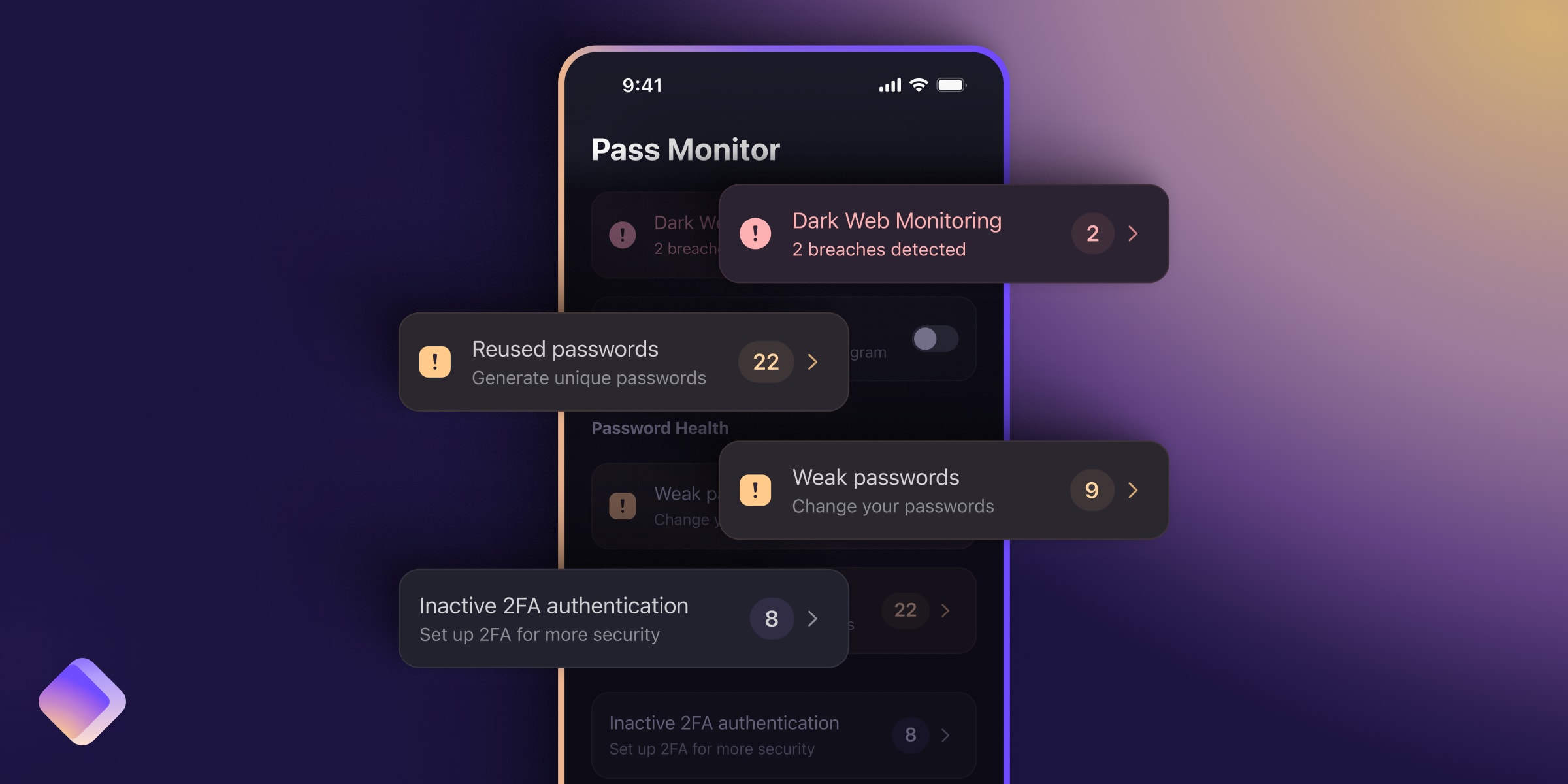
The best password managers will also alert you when you duplicate passwords across accounts, too, so you don’t fall into the trap of reusing passwords. Rather than have dozens of vulnerabilities, you have only one, and a well-used passphrase can do a great job of protecting that one, too.
Proton Pass and your password policy
We developed Proton Pass as an alternative password manager that does all the above, and then some. Not only can it manage and generate passwords, we also give you the option to generate secure passphrases, in case you need a password that’s easier to remember. It also autosuggests and autofills as you browse, making account admin a lot easier.
Proton Pass also offers your organization security in other forms, like through our hide-my-email aliases, which enter a spoofed email address when creating a new online account, offering an extra layer of anonymity. You can also subscribe to our advanced plans and get access to Proton Sentinel, an advanced program that helps protect against phishing attacks.
Most importantly, though, Proton Pass for Business has 2FA support built-in, making it much easier for your team members, and organization as a whole, to adopt this vital security tool. Instead of having to deal with cumbersome apps, all your tools are in the same place. Same security, far less hassle.
Proton Pass for Business is the perfect companion for any password policy you’re working on for your team, allowing your colleagues to securely share workplace login details. And you can manage your users from the admin panel, so you can grant or revoke access as needed, or enforce 2FA. If our features spark your interest, get started today.