Today we are officially launching Proton Mail Bridge, which brings easy-to-use email encryption to desktop email clients.
Ever since the day that we first got the idea to create Proton Mail, one of the most enduring challenges has been how to do email security right while simultaneously making encrypted email easy enough to use for normal people. Since our early days working from the CERN cafeteria(new window), we have been working tirelessly to address this specific problem.
In the years since, we have made many great strides towards creating usable encrypted email, first with Proton Mail’s webmail interface and then with our award-winning(new window) iOS(new window) and Android(new window) secure email apps. However, one of our goals has always been to bring easy-to-use encrypted email to desktop. The problem is formidable. Desktop systems encompass multiple operating systems with dozens of popular email clients with their own adherents, and virtually none of them natively speak PGP, the email encryption standard upon which Proton Mail is built.
Around two years ago, we created a small task force to tackle this challenge. Today, we are finally ready to present Proton Mail Bridge(new window).
 (new window)What is the Proton Mail IMAP/SMTP Bridge?
(new window)What is the Proton Mail IMAP/SMTP Bridge?
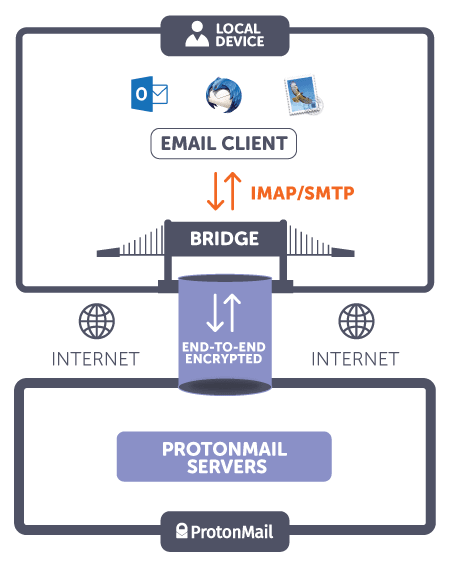
In a single sentence, Proton Mail Bridge is an application that allows you to use your Proton Mail encrypted email account with your favorite desktop email client such as Thunderbird, Apple Mail, or Outlook, while simultaneously retaining the zero-access encryption and end-to-end encryption that Proton Mail provides. The best part is that this does not require modifying your email client or making changes to your existing workflow. Use email like you have always used it, and the Bridge will automatically encrypt and decrypt messages in the background.
How does the Proton Mail Bridge work?
The Bridge is an app that you download(new window) and install locally on your desktop or laptop computer and it runs automatically in the background.
The Bridge essentially acts like a local email server (using the IMAP and SMTP protocols) and interacts with email clients also installed locally on your desktop computer. As a result, all encryption and decryption occur locally and thus the benefits of end-to-end encryption remain. The Bridge communicates with Proton Mail’s encrypted email server via our API, which supports end-to-end encryption, while email clients can communicate directly with the Bridge via standard IMAP and SMTP. In this way, standard email clients which do not natively support end-to-end encryption can support encryption without modification. Another way to think of it is that the Proton Mail Bridge translates end-to-end encrypted email data into a language that any email client can understand, thus “bridging” the gap between Proton Mail’s end-to-end encryption and your standard email client.
 (new window)
(new window)
(new window)Full-text search, multiple accounts, import/export
One of the powerful benefits of using the Bridge and email apps like Thunderbird, AppleMail, and Outlook is being able to use full-body text search within your encrypted emails. The Bridge decrypts messages as they arrive in your computer and delivers them to your desktop email client. These local copies are stored on your computer, so the search features of your desktop client work normally and you can search within your encrypted emails.
Another powerful benefit of the Bridge is being able to have multiple accounts added to an email client. For example, many users will have both a Gmail account and a Proton Mail account. In this scenario, you could simply drag messages between accounts using Thunderbird (for example). This essentially enables you to drag and drop an existing Gmail account into a new Proton Mail account as a way of doing “Account Import” (a dedicated account import and export tool is currently under development). Similarly, for users who want a backup of their Proton Mail data, most native email clients let you mass export your data and download it. You can also have multiple Proton Mail addresses and accounts in a single email client, and move messages between your Proton Mail accounts.
Threat Model
The Bridge preserves end-to-end email encryption, and also zero-access encryption (meaning that even we cannot read your emails). However, the Bridge does not protect your emails from end-point compromise (e.g. compromised laptop). Since the Bridge decrypts data locally, it’s important to ensure that your computer is safe. If someone breaks into your computer while using the Bridge, the unencrypted data could potentially be viewed as well.
During the installation process, the Bridge will auto-generate a “Bridge Password”. This Bridge Password is used to setup and configure your email clients. In this way you don’t need to trust your email client with your secret Proton Mail password.
JavaScript Cryptography and Open Source
Because the Bridge is locally installed, it is like our mobile apps in that it does not do decryption in a browser. Therefore, the Bridge also guards against the threat vector of somebody compromising the connection between you and Proton Mail in order to send you bad JavaScript code, or Proton Mail getting compromised and serving a malicious webpage to users.
Furthermore, after the technical documentation of the Proton Mail Bridge code is done, we will be releasing the source code of the Bridge, so that you can even compile it yourself instead of getting the binaries from us, so there is even less need to trust us. This is an important step in our work to eliminate Proton Mail itself as a threat vector.
Using the Proton Mail Bridge
The Bridge software is easy to set up and use. The setup process consists of:
- Installing the Bridge app
- Adding your Proton Mail account to the Bridge
- Adding your Proton Mail account to your email client (Thunderbird, Apple Mail, Outlook)
- Configuring your email client’s settings (ports, password, etc).
Currently, the officially supported email clients are Thunderbird, Apple Mail, and Outlook, on both Windows and MacOS (Linux is coming in Spring of 2018). However, in theory, any IMAP email client can work with the Bridge, and in our beta testing, many were shown to work. If you are a paid Proton Mail user, you can immediately get started here:
Finally, we would like to thank the thousands of Proton Mail users who participated in the Bridge Beta over the past year. Your support and feedback was invaluable towards bringing the Bridge to fruition, and we look forward to making Proton Mail even better for the community.
Best Regards,
The Proton Mail Team
Read the Proton Mail Bridge press release(new window)
Get a free secure email account from Proton Mail
We also provide a free VPN service(new window) to protect your privacy.
Proton Mail and Proton VPN are funded by community contributions. If you would like to support our development efforts, you can upgrade to a paid plan. Thank you for your support!