In Proton Mail v1.11 and up, we support the importing of your existing email contacts from other email service providers (ESPs).
The process takes just a few minutes and is outlined here:
Export contacts from Gmail
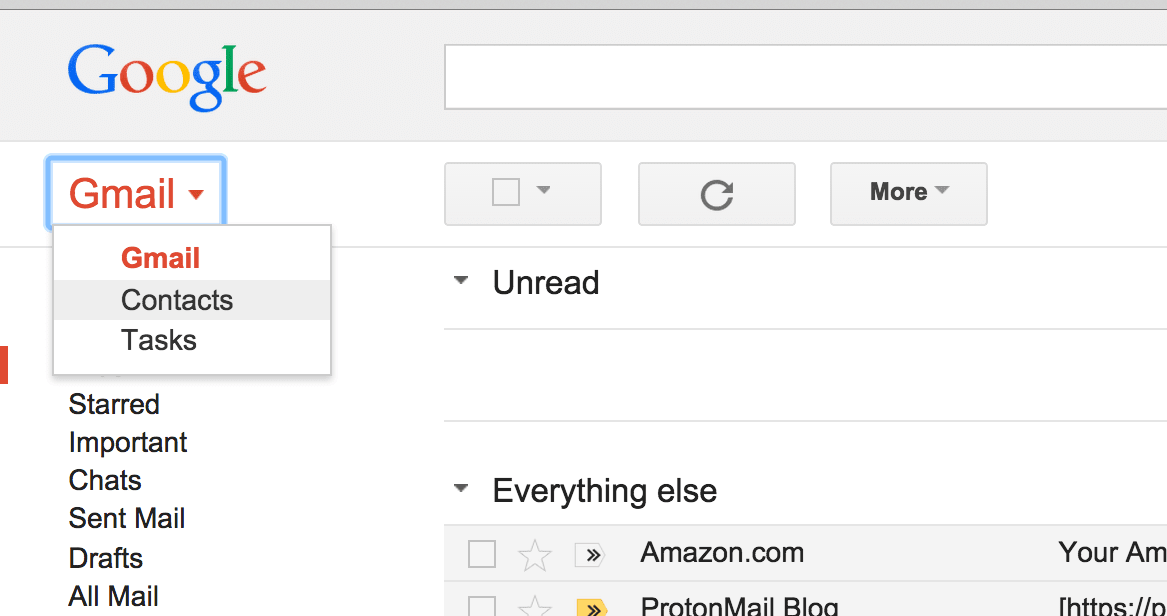
1. Log in to Gmail.
2. Go to the “Contacts” page.
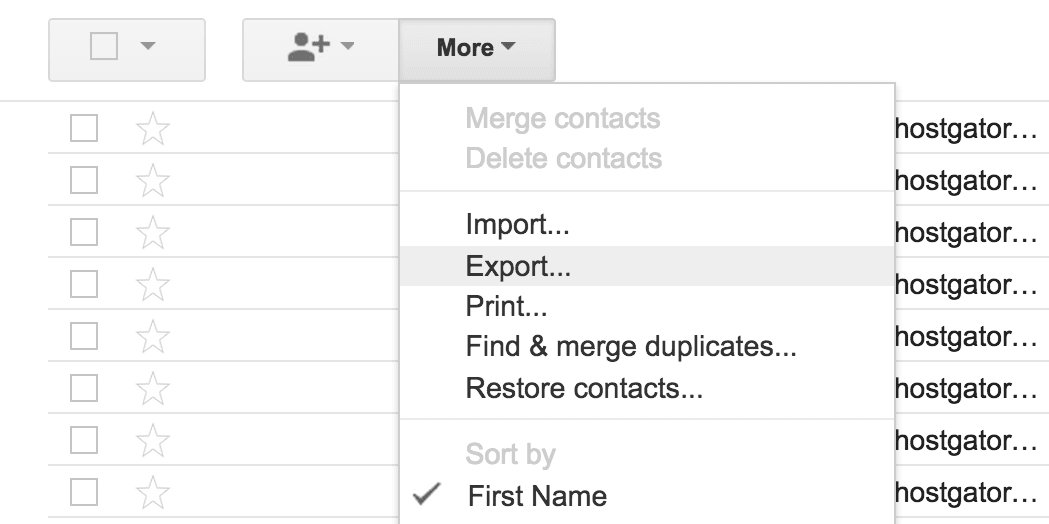
3. Click “Export”.
4. Choose a format.

Once you have exported your contacts to a file, visit your Proton Mail Contacts page to import your contacts.
We only have a guide for Gmail for now. We will update this post with additional ESP later.