This summer, we conducted a security audit to determine whether Proton is susceptible to an attack against public key cryptography, known as a batch GCD attack. As a result of our analysis, we can confirm that none of our users is vulnerable to this attack.
The attack exploits faulty sources of randomness when it comes to generating RSA keys. While this problem is relatively rare now, some older operating systems’ random number generators were not really random and sometimes generated RSA public keys that shared a prime factor. Using a special algorithm, attackers with access to a large number of public keys could potentially identify these primes and reveal secret keys. Given the growth of Proton Mail and the number of public keys that are available, we felt this was an appropriate time to run this test.
This article explains further details about why we conducted this audit and what conclusions we reached.
How batch GCD attacks work
A group of researchers discovered the batch GCD algorithm(new window) in 2012 but decided not to describe it in detail so that it could not be used to crack encryption. But within a few months, others published papers describing similar algorithms, essentially releasing instructions for hackers to execute the attack.
Batch GCD attacks are not easy to pull off. It first requires the hacker to obtain a large number of public keys. Although public keys are publicly available, it would be very difficult to collect hundreds of thousands or millions of them without anyone noticing. At Proton Mail, we have rate limits on public key requests to prevent this sort of abuse. However, it is conceivable that a sophisticated attacker with access to many IP addresses could, over time, collect a large number of public keys.
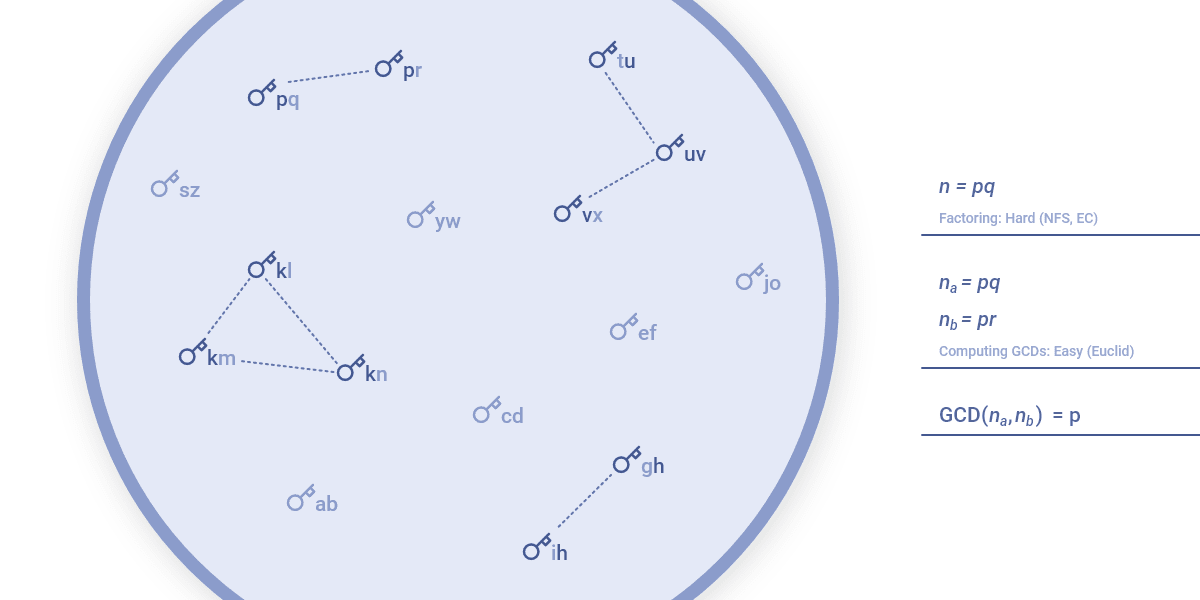
Running the batch GCD algorithm only requires a server with substantial RAM and disk space. The attack itself is not difficult to execute, and its code is freely available on GitHub. For savvy readers, this page describes how the batch GCD algorithm works(new window), but it is basically a calculation that looks for RSA moduli (i.e., composite numbers) that share prime factors. Among two RSA moduli, the greatest common divisor (GCD) is actually the common prime. If one prime is known, finding the paired secret key is simple.
Proton Mail users are safe against batch GCD attacks
Our audit sought to determine whether any of our millions of users have public keys with the same primes. If they had, they would have had the opportunity to preventatively update their keys.
The only way to find out was to run the algorithm against the public keys in our database. We did not take this decision lightly. However, we believe it would have been negligent not to test the quality of Proton public keys. If we didn’t do it, a hacker could have.
The results were very reassuring. Only 90 public keys shared primes, and all of them belonged to spam accounts, which were automatically removed by our anti-abuse systems.
The main takeaway is that even against sophisticated attacks that target public key encryption, Proton Mail remains secure.
Maintaining Proton Mail’s security
This audit is part of the continuous work we do to ensure that Proton Mail continues to deliver the privacy and security that our users expect and require. However, this job is never over. In the future, we plan to give our users the ability to require that their messages be sent externally only over TLS, to ensure your email remains secure even when it is passing through remote servers.
Our number one priority is our users’ security, and we will continue to upgrade and test our system to ensure your data stays safe.
You can get a free secure email account from Proton Mail here(new window).
We also provide a free VPN service(new window) to protect your privacy. Proton Mail and Proton VPN are funded by community contributions. If you would like to support our development efforts, you can upgrade to a paid plan(new window). Thank you for your support.
Feel free to share your feedback and questions with us via our official social media channels on Twitter(new window) and Reddit(new window).














