What was your first pet’s name? In what city were you born?
We’ve all had to answer these questions to reset a long-forgotten password, but consider how that works. Much of this information is easy to find for others (or easily forgotten by you), making it a poor defense for your most valuable online accounts, personal data, and sensitive information.
Security questions are meant to help reset passwords, reopen locked accounts, and ultimately protect your digital spaces from attacks or breaches, but such safeguarding is widely considered flawed and unreliable(new window).
A massive Yahoo data breach(new window) highlighted the perils of relying on security questions to protect your accounts. The breach exposed the personal data of half a billion million users, including their names, email addresses, phone numbers, and the security questions and answers they used for account recovery.
This article will explore why security questions are actually terrible for your security and what measures you can take to better protect your most sensitive private data.
What are security questions?
When you’re locked out of an account, it’s common to face security questions to regain access or reset passwords. This gatekeeper layer of security is common and used across many platforms, from email and social media to banking and shopping websites.
Answers to questions like “What is your mother’s maiden name?” are supposed to be information only you know or a select few — in theory, the more obscure the answer, the better the security.
However, experts have begun to question the effectiveness(new window) of this security layer due to the vulnerabilities that come with requiring people to remember information that can be forgotten, changed, or discovered by potential attackers digging around on the Internet.
Why security questions are a terrible idea
There are several reasons why leaning on security questions to protect you is a bad idea. It comes down to a pair of unfortunate realities: Potential attackers are more clever than you might think, and there’s more personal information online than you realize.
Here’s a look at why security questions are the weakest link of security measures:
- Predictability(new window): Popular security questions like “What is your favorite color?” can be too generic and easily predictable, according to the UK’s National Cyber Security Centre(new window). When the pool of possible answers is small, it’s much easier for a potential attacker to guess.
- Discoverability: In an age where people manage multiple social media accounts across several platforms, attackers can often find answers to security questions with a little digging into your public-facing profiles. They can build a profile of you based on your posts, exploiting publicly available information to bypass security measures and gain access to your account.
- Forgettability: Favorites and life details change over time, often making it difficult for you to recall information at the moment you need to. This greatly diminishes the reliability of security questions as a security tool.
The National Cybersecurity Centre encourages people to use authentication methods that are as robust as the passwords themselves and caution against relying solely on security questions(new window). Even Google released a study(new window) contending that security questions are one of the worst ways to protect your online privacy(new window).
“40% of English-speaking US users have failed to recall their answers to security questions, according to Google,” reported Time(new window). “When the questions are very difficult, such as asking for a person’s frequent flier number, the recall rate drops to 9%.”
Beware of oversharing on social media
By exploring your social media accounts, hackers can often obtain the information you use to reset passwords, particularly the answers to security questions. Make sure to consider anything you share that could contain the following information:
- Family names
- Date of birth
- Location of birth
- What school you attended
- Pet names
- Any address, current or former
- Details of your routine
What’s at stake? Your data and privacy
If the answers to your security questions are ever compromised, it can lead to widespread privacy violations.
- Identity theft: With access to something like your bank account, it wouldn’t take much work for an attacker to impersonate you, open new accounts, or commit fraud with your stolen identity(new window).
- Compromised accounts: If the answers to your security questions are exposed in a data breach, any account tied to the answers of those questions can be in danger, as it’s common for people to recycle the same ones over multiple accounts.
What are better alternative security measures?
Knowing the dangers that could come with traditional security questions, you might consider using more effective – and reliable – authentication methods.
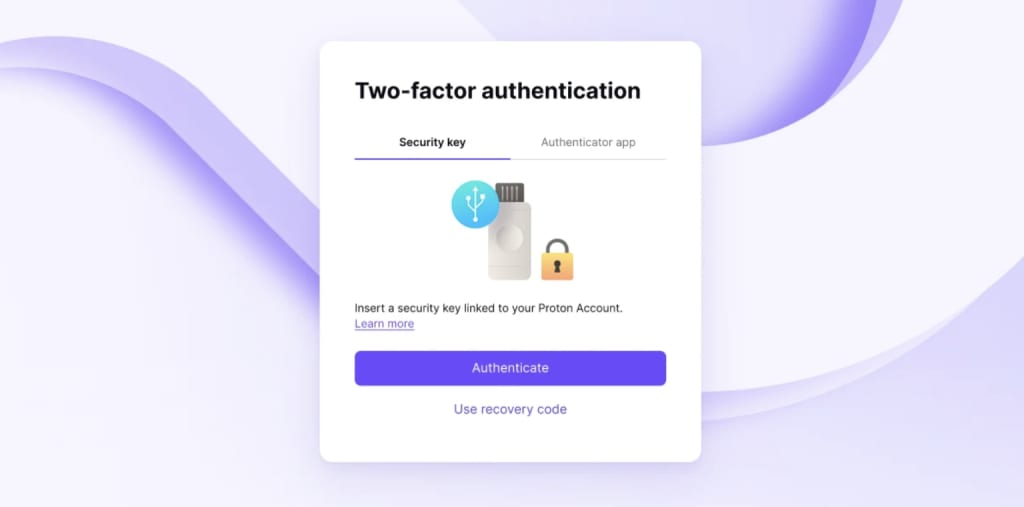
Two-factor authentication (2FA)(new window), also known as two-step verification, requires two forms of identification when you log into an account. After you input a username and password, 2FA may have you enter a unique code generated by a mobile authenticator app, plug in a security key(new window), or type in a code sent to your phone.
Here’s a look at the best forms of 2FA:
- Security key(new window): Security keys, also known as hardware keys, help prove your identity when you’re logging in to an account, app, or device. This allows you to sign in to your account using a physical key, such as a YubiKey(new window), which resembles a thumb drive. If you choose to use a 2FA key with your Proton Account, for example, you must plug in your key every time you sign in.
- Time-based one-time passwords: You can use an authenticator app on your smartphone to generate six-digit passwords that regenerate every 30 seconds to keep codes fresh and make unauthorized access to your accounts difficult for potential attackers. Using TOTP can be inconvenient, however, as it involves entering a code in a short period of time.
What about SMS messages?
Text messages are considered the least secure of 2FA options, as they are vulnerable to SIM-swapping attacks(new window). SMS is unencrypted and insecure(new window), making it easier for hackers to intercept 2FA codes. If there are multiple 2FA methods offered, SMS should be avoided.
Best practices for online security
As cybersecurity threats become more sophisticated and common, it’s important to reassess security practices and the role security questions play in our defense against such attacks. Here are two ways you can enhance your online security right now:
- Use a private and secure email service: Signing up with an encrypted email provider, such as Proton Mail, ensures all of your emails can be read only by you and your intended recipient. Proton Mail uses end-to-end encryption(new window) (E2EE), zero-access encryption(new window), and other advanced security features to protect your messages.
- Use email aliases: These let you keep your personal email addresses private. You can use a service, such as SimpleLogin by Proton, to generate distinct email addresses for your various online accounts. That way you can easily revoke an alias tied to a specific account should that account become compromised.
Put your privacy first
You can start by prosecuting your trust in security questions and using alternative tools, such as two-factor authentication and secure email services like Proton Mail to strengthen your defenses.
It’s important to use the best tools available to build a future where privacy is the default.














