What are PGP/MIME and PGP/Inline?
Proton Mail supports PGP encryption(new window) to send encrypted messages to encrypt emails(new window): PGP/MIME and PGP/Inline.
What is PGP/Inline?
One approach to encrypt an email with PGP is to encrypt everything separately. This means that the message body and attachments are individually encrypted and signed(new window).
The benefit of this approach is that your recipient can use email clients that don’t support PGP encryption and use third party tools to decrypt the message, by copying the message body and/or downloading the attachments and using a tool like gpg(new window) to decrypt each one. However, because the message body and attachments are encrypted separately, this approach leaks information about the type and name of each attachment.
For historical reasons PGP/Inline doesn’t support sending HTML messages(new window), so all PGP/Inline messages will be sent in plain text.
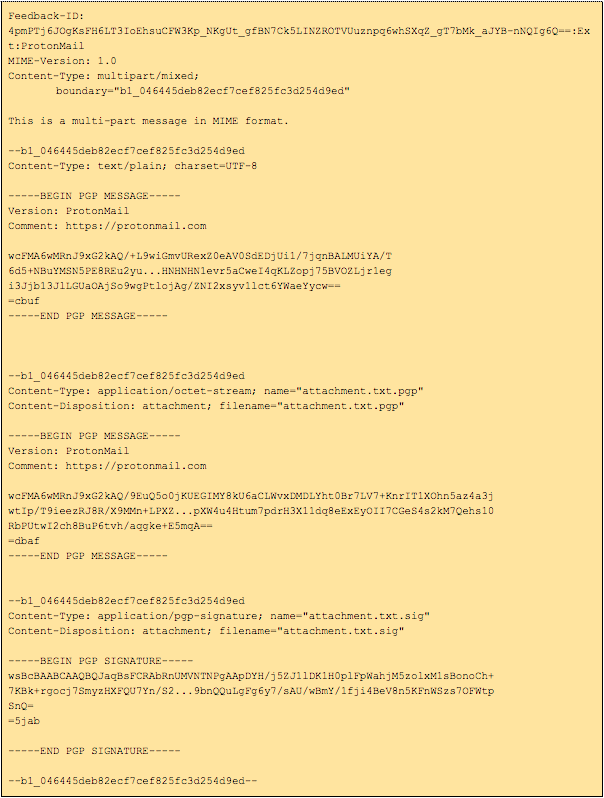
Here is a sample PGP/Inline message:
What is PGP/MIME?
A newer approach is PGP/MIME, which in contrast to PGP/Inline, PGP/MIME encrypts and signs the message, including attachments, as a whole.
An advantage to this scheme is that the message structure, like attachment metadata, is not leaked to someone who intercepts the encrypted message. PGP/MIME also tends to be less intrusive when displaying message signatures in clients that do not support PGP. However, to be able to read just the message body, it is necessary to download the whole message, including all attachments, because everything is encrypted together.
Unlike PGP/Inline, most clients support PGP/MIME in combination with HTML messages.
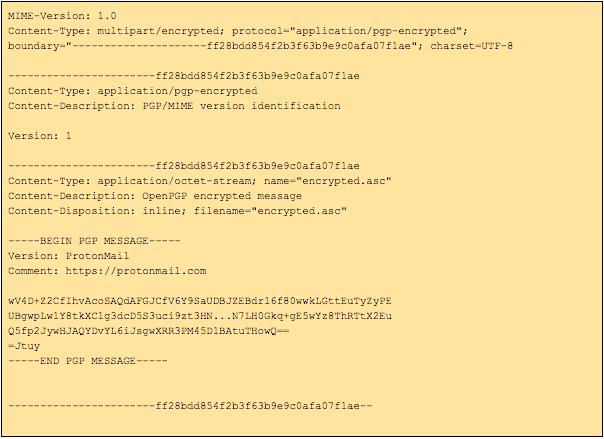
Encrypting with PGP/MIME will often generate a message like this:
As shown above, this generates one big attachment called encrypted.asc, so anybody who sees this has no information about what may be inside this message.
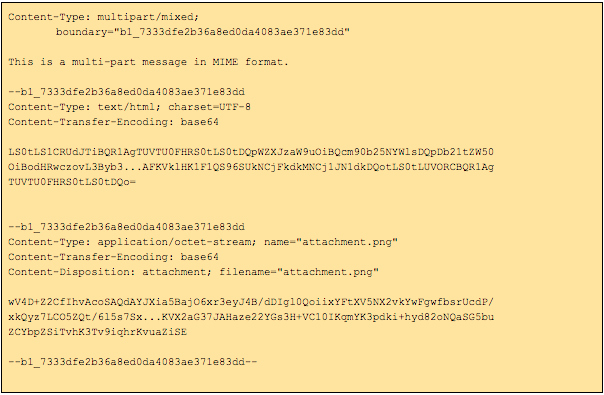
After decrypting encrypted.asc, the following data can be found: